News
-
News28 December 2023An OTT Channel provider adopts AI powered Perception Point Email Security to stop Quishing attacksFake QR Code Email Phishing Scam Beware: Fraudsters are sending mails with...
-
News23 October 2023Logix Day 2023Logix InfoSecurity celebrated its Annual Event on October 7th and 8th in...
-
News18 October 2023Celebrating Success: Logix InfoSecurity at SAARC Partner SYNC 2023We’re thrilled to share that Logix won 2 awards at Fortinet SAARC...
-
News4 October 2023Defend Against Modern Email Threats with Acronis Cyber Protect’s AI-Powered Email SecurityCyber threats are constantly evolving. Email security demands an innovative approach. Enter...
-
News14 August 2023Celebrating 24 Years of Excellence: Logix InfoSecurity’s Foundation DayOn the 16th of August, as we proudly celebrate Logix InfoSecurity's foundation...
-
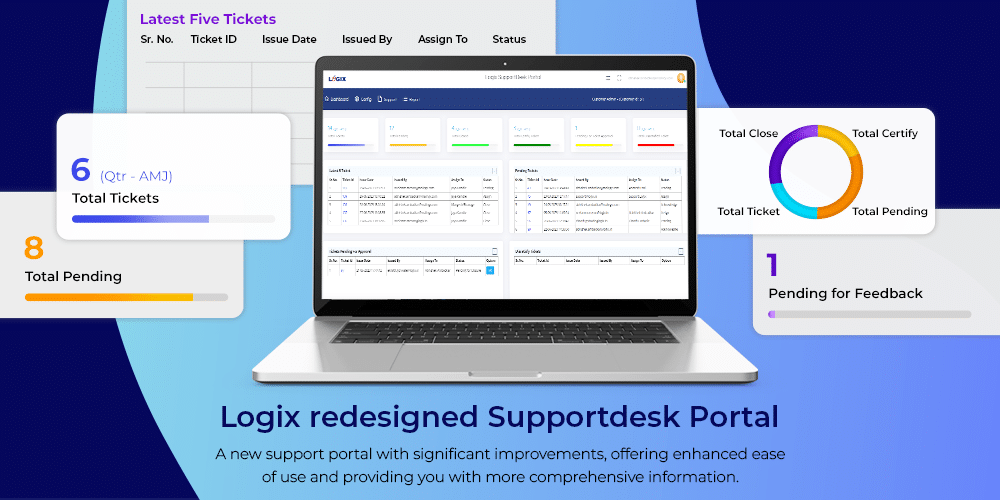
News4 July 2023Introducing the Revamped Logix SupportDesk PortalWe are thrilled to announce our newly redesigned Logix Supportdesk portal is...
-
News16 January 2023Important Licensing Changes to Microsoft India Commercial BusinessMicrosoft India is announcing Indian rupee pricelist changes to harmonize its prices...
-
News1 November 2022Logix Offers Multiple Upgrade Options for Office 365 Kiosk / F1 Plan UsersMicrosoft recently disabled support for POP / IMAP for its Office 365...
-
-
News5 August 2022Logix Wins the Fortinet Best Enterprise Partner Award 4th Time in A RowAs the African proverb says, “If you want to go fast, go...
-
Microsoft Defender for Buisness: Why Traditional Antivirus Is No Longer Enough for Businesses
For years, traditional antivirus solutions have been the default choice for business...
-
DroidLock Malware: A Growing Threat to Android Devices and Enterprise Mobility
A newly identified Android malware strain, DroidLock, highlights the increasing risk posed to...
-
Workplace Cybersecurity with Check Point Harmony
In today’s hybrid-work world, email and collaboration platforms power nearly every day-to-day activity —...
-
Phishing Simulations: A Technical Layer of Defence for BFSI Cybersecurity
BFSI organizations operate in a high-risk environment where cybercriminals aggressively target employees through social...
-
Why Secure Access Service Edge (SASE) Is a Game-Changer for Modern Enterprises
As remote work, cloud applications, and distributed teams become the norm, traditional...
-
Microsoft 365 Security: Why the Built-In Stack Shouldn’t Be Overlooked
The modern workplace depends heavily on productivity office suites. Mail, meetings, documents,...
-
Blog 11 December 2025 Workplace Cybersecurity with Check Point Harmony -
Blog 11 December 2025 Phishing Simulations: A Technical Layer of Defence for BFSI Cybersecurity -
Blog 10 December 2025 Why Secure Access Service Edge (SASE) Is a Game-Changer for Modern Enterprises -
Blog 3 December 2025 Microsoft 365 Security: Why the Built-In Stack Shouldn’t Be Overlooked -
Blog 3 December 2025 Why DMARC Matters — And Why Your Business Can’t Ignore It -
Blog 11 November 2025 India’s Digital Transformation Needs Secure Collaboration
-
Workplace Cybersecurity with Check Point HarmonyIn today’s hybrid-work world, email and collaboration platforms power nearly every day-to-day activity —...
-
Phishing Simulations: A Technical Layer of Defence for BFSI CybersecurityBFSI organizations operate in a high-risk environment where cybercriminals aggressively target employees through social...
-
Why Secure Access Service Edge (SASE) Is a Game-Changer for Modern EnterprisesAs remote work, cloud applications, and distributed teams become the norm, traditional...
-
Microsoft 365 Security: Why the Built-In Stack Shouldn’t Be OverlookedThe modern workplace depends heavily on productivity office suites. Mail, meetings, documents,...
-
Why DMARC Matters — And Why Your Business Can’t Ignore ItIn the past months, several Indian companies have lost crores to email...
-
India’s Digital Transformation Needs Secure CollaborationAs enterprises continue to accelerate their digital transformation journeys, the priorities have shifted...