News
Explore insights, trends, and expert updates on cybersecurity, cloud, and IT innovations to keep your business secure and future-ready.
-
News2 January 2026Fake e-Challan Websites: How Phishing Campaigns Are Targeting Indian DriversIndian motorists are being targeted by a large-scale cyber fraud campaign that...
-
News16 December 2025DroidLock Malware: A Growing Threat to Android Devices and Enterprise MobilityA newly identified Android malware strain, DroidLock, highlights the increasing risk posed to...
-
News27 November 2025Rising “Do You Remember Me?” Scam: A Wake-Up Call for BusinessesA fresh global alert from Google warns of a surging phishing-as-a-service campaign:...
-
News14 November 2025Preventing QRR-style Phishing: Make Microsoft 365 Privately AccessibleThe Quantum Route Redirect (QRR) phishing campaign has once again exposed how...
-
News12 November 2025Safeguarding Organizational Data Amid Rising Attrition and Intentional Data DeletionWith increasing employee attrition, organizations are facing new risks in managing and...
-
News12 November 2025The Dr. Reddy’s Email Fraud Case – A Wake-Up Call for Business Email SecurityIn a recent incident reported by Mint, hackers successfully duped Dr. Reddy’s...
-
News8 July 2025Logix Takes Its Stellar Customer Support to the Next LevelSupport delays can slow down your business - that’s why we’ve introduced...
-
News5 May 2025Get Instant Support with the New Logix AI AssistantAt Logix, we are constantly working to make your experience better, faster,...
-
News10 April 2025Fortinet Partner of the Year 2024 – Fortinet ACCELERATE25Logix has been awarded the Fortinet Partner of the Year 2024 (India...
-
News19 March 2025How Barracuda Solves the Outlook Mailbox Capacity ProblemIs Your User Struggling with Outlook Due to Mailbox Reaching its Storage...
-
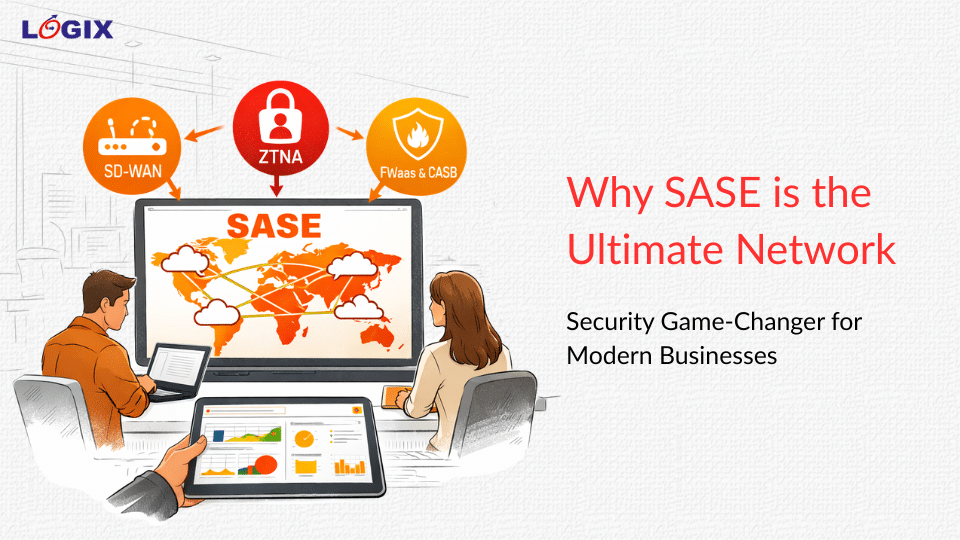
Why SASE is the Ultimate Network Security Game-Changer for Modern Businesses
The traditional network perimeter has not just moved; it has effectively dissolved....
-
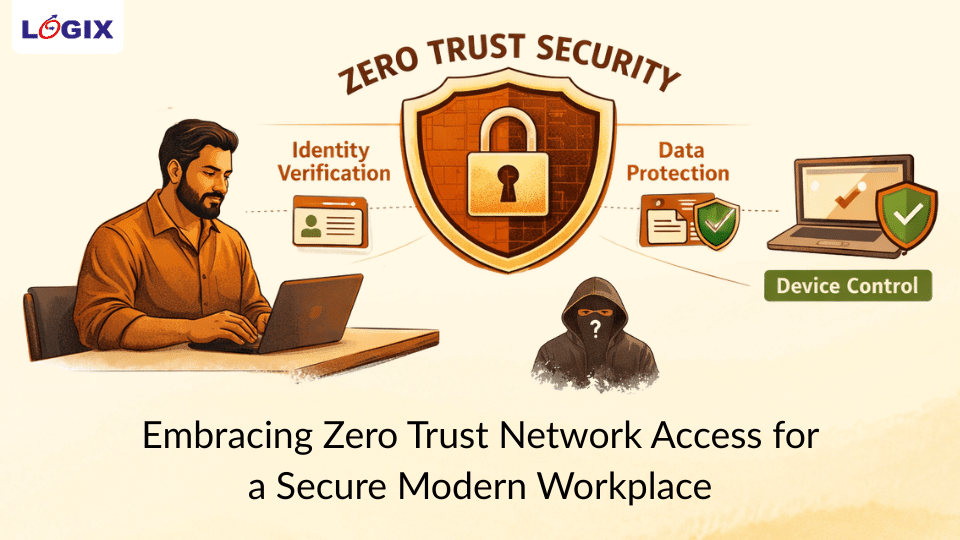
Embracing Zero Trust Network Access for a Secure Modern Workplace
The modern workplace is no longer confined to a single office network....
-
Strengthen Email Security with DMARC: Protect Your Domain from Fraud
Why DMARC Is Essential for Protecting Your Domain from Email Fraud Email...
-
The Mission-Critical Inbox: Why Dedicated Transactional Email is a Business Imperative
The Mission-Critical Inbox: Why Dedicated Transactional Email is a Business Imperative In...
-
Forex Card Fraud Incident Highlights the Growing Risk of Data Exposure
Recent reports of unauthorized international transactions on forex cards issued by Yes...
-
Is Your Critical Data Is Truly Safe?
Cybersecurity breaches do not always begin with sophisticated malware or complex exploits....
-
Blog 17 March 2026 Why SASE is the Ultimate Network Security Game-Changer for Modern Businesses -
Blog 17 March 2026 Embracing Zero Trust Network Access for a Secure Modern Workplace -
Blog 13 March 2026 Strengthen Email Security with DMARC: Protect Your Domain from Fraud -
Blog 13 March 2026 The Mission-Critical Inbox: Why Dedicated Transactional Email is a Business Imperative -
Blog 6 March 2026 Forex Card Fraud Incident Highlights the Growing Risk of Data Exposure -
Blog 3 March 2026 Is Your Critical Data Is Truly Safe?
-
Why SASE is the Ultimate Network Security Game-Changer for Modern BusinessesThe traditional network perimeter has not just moved; it has effectively dissolved....
-
Embracing Zero Trust Network Access for a Secure Modern WorkplaceThe modern workplace is no longer confined to a single office network....
-
Strengthen Email Security with DMARC: Protect Your Domain from FraudWhy DMARC Is Essential for Protecting Your Domain from Email Fraud Email...
-
The Mission-Critical Inbox: Why Dedicated Transactional Email is a Business ImperativeThe Mission-Critical Inbox: Why Dedicated Transactional Email is a Business Imperative In...
-
Forex Card Fraud Incident Highlights the Growing Risk of Data ExposureRecent reports of unauthorized international transactions on forex cards issued by Yes...
-
Is Your Critical Data Is Truly Safe?Cybersecurity breaches do not always begin with sophisticated malware or complex exploits....