-
Blog20 February 2026Embracing Zero Trust Network Access for a Secure Modern WorkplaceThe modern workplace is no longer confined to a single office network. Employees work remotely, access cloud applications...
-
Blog20 February 2026BDR Cloud: Ensuring Business Continuity When It Matters MostData is one of the most valuable assets in any organization. Yet data loss can occur in many...
-
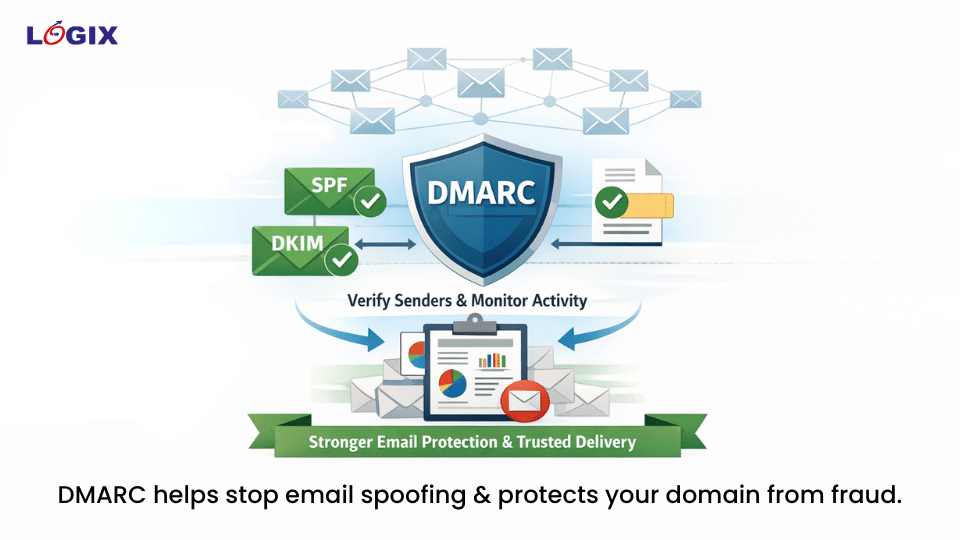
Blog18 February 2026DMARC Email Security: Protect Your Domain from Spoofing and Email FraudEmail continues to be one of the most exploited channels for cybercrime. Attackers frequently target domains that lack...
-
Blog18 February 2026Check Point External Risk Management: Securing What Lies Beyond the PerimeterTraditional cybersecurity strategies focus heavily on protecting what sits inside the network—endpoints, firewalls, servers, and internal applications. But...
-
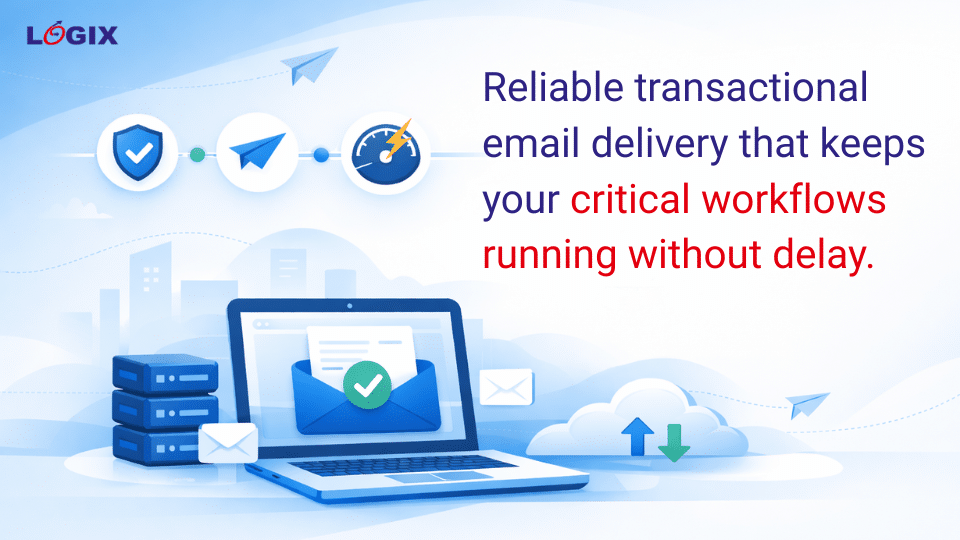
Blog10 February 2026ZatpatMail: Instant, Reliable Transactional Email DeliveryTransactional emails are the backbone of digital business operations. From OTPs and password resets to order confirmations, system...
-
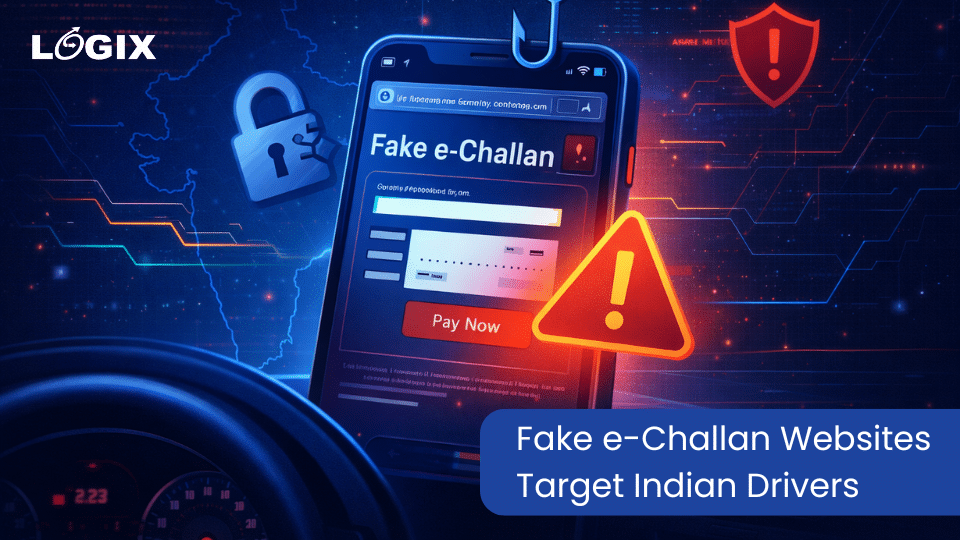
News2 January 2026Fake e-Challan Websites: How Phishing Campaigns Are Targeting Indian DriversIndian motorists are being targeted by a large-scale cyber fraud campaign that exploits trust in official traffic enforcement...
-
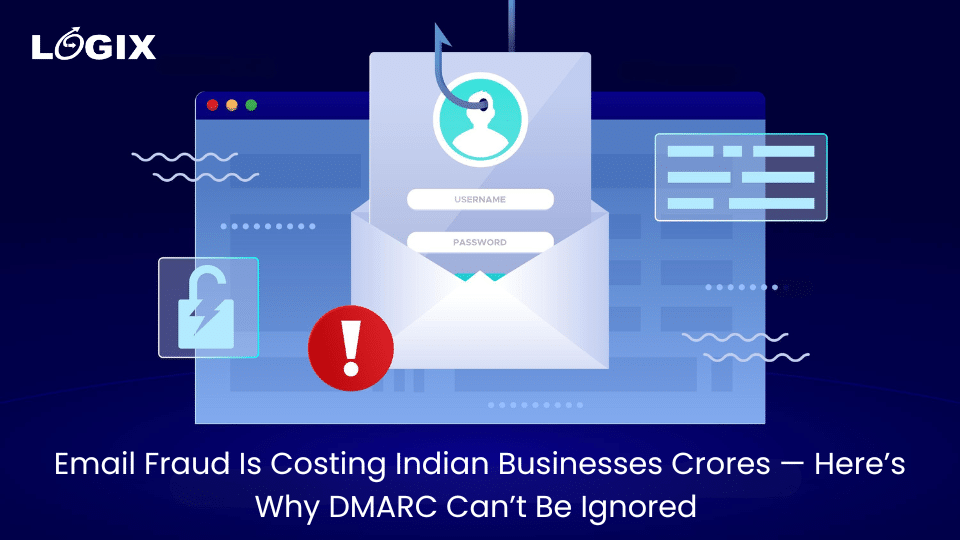
Blog24 December 2025Email Fraud Is Costing Indian Businesses Crores — Here’s Why DMARC Can’t Be IgnoredEmail fraud is no longer an isolated cyber incident. It has become a recurring and expensive threat for...
-
Blog24 December 2025Microsoft 365 Business Premium: Built-In Security for the Modern WorkplaceModern businesses need more than just productivity tools. With distributed teams, cloud-based work, and increasing cyber threats, security...
-
Blog19 December 2025Microsoft Defender for Buisness: Why Traditional Antivirus Is No Longer Enough for BusinessesFor years, traditional antivirus solutions have been the default choice for business security. They scan for known threats,...
-
News16 December 2025DroidLock Malware: A Growing Threat to Android Devices and Enterprise MobilityA newly identified Android malware strain, DroidLock, highlights the increasing risk posed to mobile devices by ransomware-style attacks. Reported...
Embracing Zero Trust Network Access for a Secure Modern Workplace
20 Feb 2026